Embed This Image On Your Site (copy code below):
Support: 800-699-0925 Sales: 800-481-1984
by SysArc
Embed This Image On Your Site (copy code below):
DoD Prime Contractors: We can setup a 3rd party validation service for your supply chain that includes a compliance Assessment against the NIST 800-171 controls for your subcontractors with a resulting risk score and remediation recommendations to get them to compliance.
DoD Subcontractors: We have developed a low-cost solution to help small subcontractors get compliant quickly and stay compliant without breaking the bank.
We perform a detailed assessment of your current network and compare this with the cyber security controls required in NIST SP 800-171. We then prepare an SSP and POAM so that you can provide documented evidence to the DoD or your Prime that you’re on your way towards compliance. This step then serves as the basis for creation of the remediation plan.
In this step the items called out in the POAM need to be addressed. Depending on the current state of your IT systems, this can be as simple as implementing multi-factor authentication and security awareness training or as complex as refreshing an entire aging infrastructure.
Ongoing advanced cybersecurity monitoring and incident response capabilities are required to remain compliant. If a cyber incident occurs you must notify the DoD through the DIBNet Portal (https://dibnet.dod.mil/portal/intranet/) within 72 hours. You must also constantly assess and maintain the NIST 800-171 controls over time as systems change and fall out of alignment.
How we’ve helped DoD Contractors across the U.S. comply with DFARS / NIST 800-171

Wilcoxon Sensing Technologies is a leading supplier for high performance vibration monitoring and sensing solutions. Their top quality vibration sensors and accessories are trusted by OEMs, major manufacturers, and important organizations around the world including the Department of Defense. The DoD has a cyber security requirement (DFARS 252.204-7012) based on the NIST SP 800-171 controls for all suppliers to comply with in order to continue doing business with them. Learn how SysArc helped them become compliant…

Newark Wire Cloth Company (NWC) is a small manufacturer that specializes in wire cloth filters based in Newark, New Jersey. They weave these filters in order to provide vital tools in the aerospace industry and military aviation. NWC’s prime contractor required them to become compliant to continue being a supplier due to the DFARS regulation and its flow-down clause. Learn how SysArc helped them become compliant…
Read our publications on DFARS / NIST 800-171 Compliance
On September 29, the Defense Acquisitions Regulation System released a new Interim Rule to supplement current DFARS regulations. While the Department of Defense is working... Read more →
SysArc’s primary aim is to provide DoD suppliers with Cybersecurity Maturity Model Certification (CMMC) readiness services and solutions, which is why we have dedicated our... Read more →
This guide was written to help DoD contractors and subcontractors quickly understand what is required of them to take proper action after they either suspect... Read more →
We work with the Department of Defense (DoD) Contractors all over the United States and help them navigate the complexities of DFARS and NIST 800-171... Read more →
Broadly speaking, the U.S. Government defines Controlled Unclassified Information (CUI) as any information that requires safeguarding or dissemination controls pursuant to and consistent with applicable... Read more →
The Department of Defense’s final guidance requires the review of a System Security Plan (SSP) in the assessment of contract solicitation during the awards process.... Read more →
The U.S. Department of Defense (DoD) has released final guidance on assessing contractor compliance with NIST SP 800-171 during the contract award process. Based on... Read more →
A common question that small DoD contractors and subcontractors have is whether they are subject to the requirements of the Defense Federal Acquisition Regulation Supplement.... Read more →
The Washington Post has reported that The Pentagon has developed a new strategy to protect its supply chain from cyber crime and foreign interference. As well... Read more →
by SysArc

If you’re in need of getting your company’s processes and data security GDPR compliant, consulting a Managed Security Service Provider (MSSP) can help your company navigate the complicated road towards compliance. This article will focus specifically on GDPR compliance and what you can expect from a GDPR consultant. However, the processes MSSPs use to help their clients become GDPR compliant, apply to other compliance mandates as well.
General Data Protection Regulation (GDPR) is a collection of data protection laws that expand the scope of the 1995 Data Protection Directive. GDPR focuses on preserving the digital rights of people living in the European Union.
Some of the key regulations in GDPR include requirements to:
When GDPR goes into effect on May 25, 2018, companies around the world will need to change their approaches to protecting the privacy of personal data. GDPR doesn’t just apply to organizations operating within the EU. Any organization that provides services to individuals or companies within the EU will need to follow the updated regulations.
The expanded requirements of GDPR will put a significant burden on many companies and organizations. Failing to meet the requirements, however, can lead to penalties that include fines up to €20 million (USD 24.75 million) or 4 percent of a company’s annual global turnover, whichever is greater.
The possibility of losing so much money in fines should encourage more companies to hire Managed Security Service Provider (MSSP) consultants that can oversee processes and make sure they align with the new regulations. At SysArc, we make sure our clients have the information that they need to follow GDPR so they can serve their customers well and avoid penalties.
SysArc’s MSSPs start their jobs by performing gap analyses designed to discover inadequate processes that may not meet the EU’s updated regulations. Taking a close look at your network and procedures is the first step to ensuring compliance.
The results of our gap analyses may reveal issues with:
Without a gap analysis, it’s impossible to know what changes an organization needs to make before it meets the EU’s latest regulations. The professionals at SysArc use their findings to create remediation plans that will correct any problems and keep our clients in line with GDPR.
SysArc’s remediation plans provide careful documentation of processes that don’t meet today’s standards. Having a well-researched plan also makes it easier for our clients to make necessary changes to their systems.
Once we help clients meet GDPR standards, we provide legal documentation that proves compliance. This documentation provides legal protection from potential fines. Instead of taking risks, companies should make sure they have as much protection as possible. Otherwise, they could find themselves spending millions in court costs and fines.
Some international companies based in the United States don’t know that they have to comply with Europe’s new standards. This misunderstanding puts them at serious financial risk.
Outsourcing to an MSSP that specializes in GDPR compliance offers several benefits. At the very least, SysArc can help our clients save time and money while avoiding the headache of conducting in-depth analyses. Click here to sign up for a free GDPR compliance Assessment by SysArc.
https://www.eugdpr.org/key-changes.html
https://www.csoonline.com/article/3202771/data-protection/general-data-protection-regulation-gdpr-requirements-deadlines-and-facts.html
https://www.itgovernance.co.uk/shop/product/gdpr-gap-analysis
by SysArc
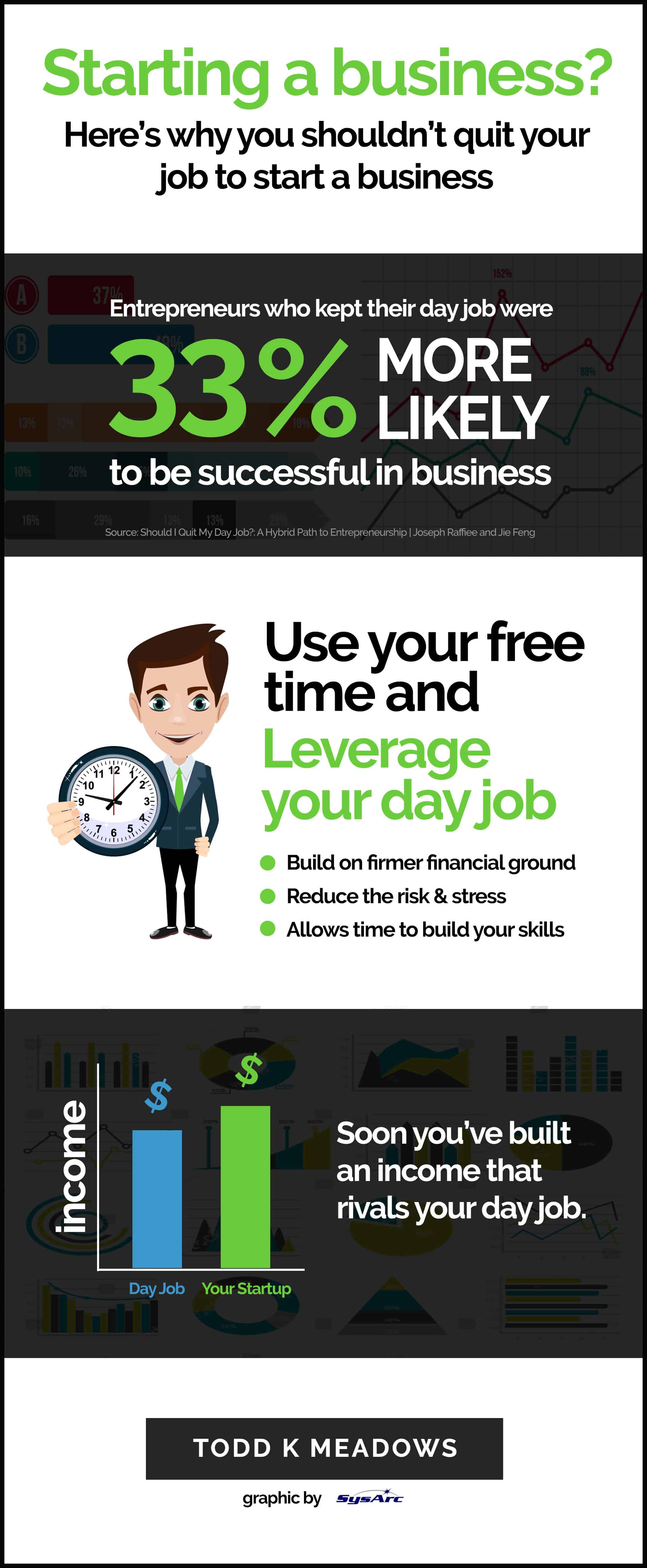
Source: http://www.toddkmeadows.com/crunchdunk-blog/why-you-shouldnt-quit-your-job-to-start-a-business
Embed This Image On Your Site (copy code below):
by SysArc

https://dmz.ryerson.ca/startup-advice-2018/
Embed This Image On Your Site (copy code below):
by SysArc

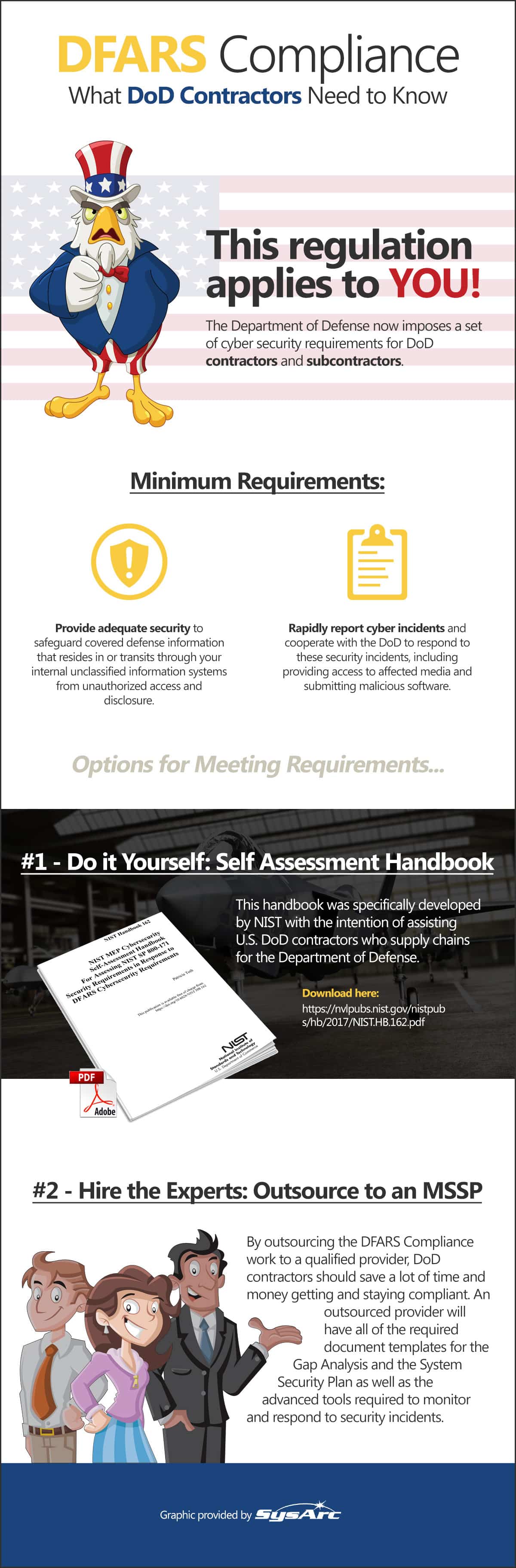
The Defense Federal Acquisition Regulation Supplement (DFARS) is a set of cybersecurity regulations that the Department of Defense (DoD) imposes on external contractors and suppliers. If you feel unsure about how to meet these cybersecurity controls, read on. I’ll explain how a managed security service provider (MSSP) can help you meet the requirements.
Since December 31, 2017, all DoD contractors and suppliers have been required to meet cybersecurity standards in 14 separate areas:
Each area has specific security requirements that contractors and suppliers are obliged to meet. Even small manufacturers are required to provide adequate security to safeguard sensitive information, as well as rapidly report cyber incidents to DoD.
For many small businesses, the most effective way to meet the requirements of DFARS is to outsource the task to a managed security service provider. Remember that you remain ultimately responsible for ensuring that your company meets the DFARS requirements, so it is essential to choose a service provider you are sure you can trust.
By outsourcing the DFARS Compliance work to a qualified provider you should save a lot of time and money getting and staying compliant. An outsourced provider will have all of the required document templates for the Gap Analysis and the System Security Plan as well as the advanced tools required to monitor and respond to security incidents. They will also have the resources required to perform the remediation steps required to become compliant.
When you choose to work with SysArc as your MSSP, the first thing we do is to perform a Gap Analysis. The purpose of this step is to see how your current cybersecurity status compares to the requirements you need to meet. We can work out what remediation work needs to be done to bring you up to compliance standards. We will create a remediation plan, detailing how we plan to bring your company up to speed, and implement the work after you have approved the plan.
Reaching compliance is only the first step in meeting the requirements set out by the DoD in DFARS. Once we have helped you to achieve compliance, SysArc works hard to monitor your security status. We keep track of cyber incidents and report them in line with DFARS regulations.
Don’t make the mistake of thinking that your business will never experience a potential cybersecurity breach. The cybersecurity landscape is constantly changing, with hackers continually coming up with new ways to steal valuable and sensitive information. DoD will not necessarily penalize businesses that experience potential breaches, as long as you meet the reporting requirements. Specifically, you must report all potential breaches to DoD within a maximum of 72 hours of discovering the incident. You can report online using DoD’s online tool or let your MSSP handle this important part of ensuring your business complies with DFARS reporting requirements.
If you need help ensuring your business complies with DFARS, outsourcing to an MSSP like SysArc can be a convenient way to meet the requirements. Get in touch with SysArc today to find out more about our service.
https://www.nist.gov/mep/cybersecurity-resources-manufacturers/dfars800-171-compliance
http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-171r1.pdf
All contractors working for DoD, even subcontractors must comply with DFARS 252.204.7012. This clause is in direct response to data breaches and cybersecurity threats and will be part of DoD contractor responsibility going forward. Each DoD contractor must meet technical and procedural controls spelled out by the National Institute of Standards and Technology (NIST) in Special Publication (SP) 800-171.
In 2020, all contractors working for the DoD, even subcontractors must pass a CMMC Audit to ensure appropriate levels of cybersecurity controls and processes are adequate and in place to protect controlled unclassified information (CUI) on DoD contractor systems. We help DoD contractors prepare for their CMMC audit.
Used as the security control framework for DFARS and CMMC, NIST 800-171 is a set of cybersecurity controls designed by the National Institute of Standards and Technology. We help companies navigate the complexities of this framework and efficiently implement the controls into their IT systems.
FISMA was introduced to reduce risks involving federal information and data while also managing federal spending on information security programs and procedures. The importance of FISMA is summarized as a means to protect sensitive information in a timely and costly manner. To be FISMA compliant, companies must follow a FISMA Certification Process that begins with meeting the guidelines set in place by NIST. Adherence to these guidelines is crucial for FISMA compliance.
The Sarbanes-Oxley Act came into force in July 2002 and introduced major changes to the regulation of corporate governance and financial practice. It is named after Senator Paul Sarbanes and Representative Michael Oxley, who were its main architects, and it set a number of non-negotiable deadlines for compliance.
This framework provides security controls for securing federal information systems. We help organizations navigate the complexities of this framework and efficiently implement the controls into their IT systems.
The Payment Card Industry Data Security Standard (PCI DSS) is an information security standard for organizations that handle branded credit cards from the major card schemes. The PCI Standard is mandated by the card brands and administered by the Payment Card Industry Security Standards Council.
These reports are intended to meet the needs of a broad range of users that need detailed information and assurance about the controls at a service organization relevant to security, availability, and processing integrity of the systems the service organization uses to process users’ data and the confidentiality and privacy of the information processed by these systems.
by SysArc

The Defense Federal Acquisition Regulation Supplement, or DFARS, is a set of security standards created by the Department of Defense to protect information handled by external contractors. These rules apply to all contractors with the DoD who “process, store or transmit” Controlled Unclassified Information (CUI).
The two foundational points of DFARS are adequate security of information and rapid reporting of any breach.
Information security standards are broken down into 14 areas of focus:
Each of the points above is detailed and explained in an 83-page document entitled NIST Special Publication 800-171. This document, in turn, references two other documents that explain each point in greater detail.
With respect to incident reporting, time is of the essence. Any data breach must be reported to the DoD within 72 hours of its discovery. The fine print of the law specifies exactly what constitutes a reportable incident, including any unauthorized access to information or any loss of control of information. There are detailed transparency guidelines that govern how such a business is required to cooperate with a DoD investigation.
All contractors who have any exposure to CUI must be very familiar with the full detailed set of rules and requirements. Within 30 days of being awarded a contract, the company must produce a written report of any areas in the DFARS standards that they are not fully in compliance with. Through the contracting officer, these companies have the right to propose alternate security measures, as long as these measures are at least as stringent as those required by DFARS.
The DoD is well aware that many small manufacturers aren’t equipped to comply with highly detailed cybersecurity requirements in-house. Therefore, they specifically allow these functions to be outsourced. Costs incurred in meeting these requirements may sometimes be recoverable, and details about this possibility are also available from the DoD. Cloud data storage providers must meet a set of standards called the FedRAMP “moderate” security requirements. They must also comply with all incident reporting and other requirements.
If you’d like to learn more about outsourcing your DFARS compliance to a cybersecurity company, get a Free Compliance Assessment.
https://www.nist.gov/mep/cybersecurity-resources-manufacturers/dfars800-171-compliance
http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-171r1.pdf
Wilcoxon Sensing Technologies is a leading supplier for high performance vibration monitoring and sensing solutions. Their top quality vibration sensors and accessories are trusted by OEMs, major manufacturers, and important organizations around the world including the Department of Defense. The DoD has a cyber security requirement (DFARS 252.204-7012) based on the NIST SP 800-171 controls for all suppliers to comply with by December 31, 2017 in order to continue doing business with them.
Wilcoxon had completed a Gap Analysis for the DFARS requirement and hired SysArc to perform the remediation work required to become compliant and to do the ongoing cyber security monitoring and incident response for the corporate network. The remediation effort included a complete network refresh to bring the environment up to date, creating a System Security Plan and rolling out a cyber security awareness training program for the entire staff. In addition, SysArc is managing the ongoing security monitoring and threat detection in a remote Security Operations Center (SOC) for Wilcoxon in order to keep the bad guys at bay while maintaining compliance with the DFARS requirements.
Wilcoxon has a new, highly secure network infrastructure that will increase the productivity of its work force and comply with the DFARS requirements, resulting in continued success in winning contracts with a major customer. The ongoing monitoring, training and threat detection will reduce the risk of a security incident occurring and be much better prepared to deal with a cyber security attack if it happens.
by SysArc

The Defense Federal Acquisition Regulation Supplement (DFARS) applies to all Department of Defense (DoD) contractors with access to Controlled Unclassified Information (CUI). This supplement details the general requirements and identifies the types of information that need additional controls. NIST SP 800-171 is the document that details the security requirements to keep that information safe.
If you want to stay active as a DoD contractor, you must be up to date on the required security methodologies. That can be a tough challenge when operating with little to no in-house IT support. However, the DoD specifically says that “Small manufacturers may use subcontractors and/or outsource information technology requirements, but they are responsible for ensuring that these entities they use to meet the cybersecurity standards.” This means that you don’t have to take direct ownership of all security updates. The right partner can enable you to focus on your business, while the IT company worries about securing your networks.
While data security is an increasingly important field, the DoD has kept the requirements on contractors straightforward and reasonable. To meet the minimum requirements, you must:
1. Provide adequate security to safeguard covered defense information that resides in or transits through your internal unclassified information systems from unauthorized access and disclosure.
2. Rapidly report cyber incidents and cooperate with the DoD to respond to these security incidents, including providing access to affected media and submitting malicious software.
While that sounds straightforward and easy to meet in-house, the term adequate security can cover a lot of ground. The DoD references 14 different areas with individual minimum security requirements. These include:
When your area of expertise and the services provided to the DoD fall outside of the technical, meeting this level of required security can be challenging with existing resources. After all, “Meeting the SP 800-171 is not a one-time fix, rather it is a continuous assessment, monitoring and improvement process.”
That means a considerable number of man-hours devoted solely to ensuring that your business remains compliant with constantly evolving security requirements. Thankfully, the DoD understands the challenge and allows for the use of subcontractors. Data breaches happen even in the most secure computing environments. Working with a security-centric third-party provider like SysArc can give you access to the additional security required without a massive capital investment to develop internal controls and cybersecurity departments.
Even when your systems meet or exceed the minimum requirements for DoD contractors, breaches happen. In 2017, sensitive information was found on an unsecured Amazon server. Not only was the data unencrypted, you didn’t even need a password to gain access. While this isn’t an actual intrusion into a protected system, it easily demonstrates the need for tighter controls over sensitive information. To help with those controls, the DoD now requires rapid reporting on all intrusions and potential security threats. Rapid reporting means within 72-hours of the discovery. While the DoD makes reporting easy using this link, getting together all of the needed information could be a challenge without a cybersecurity expert on hand to help.
Creating internal security systems that meet all 14 areas of required security minimums for the DoD would not only be cost prohibitive, it would take a lot of time. Since all contractors are required to meet these standards before starting work, and thus collecting invoices, that’s a substantial upfront investment with little guarantee of eventual profit. Third-party providers like SysArc already have the security in place to meet the minimum requirements.
If you need cloud-based services, their systems are compliant. If your on-the-ground systems need updating, instead of devoting every in-house IT resource you have, you can rely on their security options.
A large portion of DFARS/NIST 800-171 requirements falls under the heading of reporting and auditing.
Essentially, you go from underprepared to ready for DoD contract requirements quickly and seamlessly. Best of all, as a subcontractor solely on board for IT services, you can scale up or down depending on your needs. If you choose not to continue with DoD contracting and no longer need that level of security, downgrading is simple. If you scale up your contracts and expand business operations, your security scales with you.
Sources:
https://www.nist.gov/mep/cybersecurity-resources-manufacturers/dfars800-171-compliance
https://dibnet.dod.mil/portal/intranet/
https://www.sysarc.com/services/managed-security-services/
https://thenextweb.com/security/2017/05/31/department-defense-data-discovered-unprotected-amazon-server/
https://www.nist.gov/mep/cybersecurity-resources-manufacturers/dfars800-171-compliance
https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-171.pdF